Last Updated on May 30, 2024 by Arnav Sharma
What is gMSA?
A gMSA, or group Managed Service Account, is a type of managed service account that was introduced in Windows Server 2012. This type of account is designed to provide a secure and convenient way to manage Windows services and applications that run on multiple Windows Server systems. The main benefit of using this type of account is that it eliminates the need for administrators to manually create and maintain individual service accounts for each server, reducing administrative overhead and increasing security.
Group Managed Service Accounts (gMSA) are service accounts that provide a secure and centralized way to manage the security credentials of user accounts, service principals, and applications. With gMSAs, you can use a key distribution service to store the passwords and automatically rotate them on a regular basis. This helps to ensure that the service account security is always maintained even if one of the users or services changes their password. Additionally, Windows has an Active Directory Module for Windows PowerShell, allowing administrators to create and manage gMSAs in their environment easily. Using gMSAs provides organizations with an added layer of security by limiting who can access the account credentials and making it easier to perform audits on services using these accounts.
The gMSA can be used with any Microsoft application or service that runs on a domain-joined computer, such as IIS web servers and SQL databases. It also works with other third-party applications, such as Oracle database servers. To set up gMSA, administrators will need access to Active Directory Domain Services (AD DS) to create the account, which will then be replicated throughout the environment. Once created, the administrator can assign rights and privileges through security policies within AD DS. Admins can also use Group Policy Objects (GPOs) to configure settings related to the gMSA to control how it should function in their environment.
Benefits of gMSA
1. One of the primary benefits of gMSA is its improved manageability. It eliminates the need for a service account to run services and applications across multiple domain-joined machines, greatly reducing the complexity of managing these accounts. This is especially beneficial in large enterprises where hundreds or even thousands of servers run different services and applications requiring authentication from domain-joined machines.
2. Another advantage to gMSA is its increased security posture compared to regular service accounts. Since only one account is used for all services and applications, it restricts access to privileged resources, reducing the chance of unauthorized access or manipulation by malicious actors. Furthermore, gMSA also helps prevent credential theft since it uses Kerberos delegation instead of plaintext passwords stored on individual systems.
3. Lastly, gMSA provides additional flexibility with its ability to delegate credentials between domain controllers without needing manual intervention from administrators or engineers whenever an update is needed. This level of automation makes it easier for organizations to maintain secure and up-to-date authentication processes while also saving time and resources in the long run.
How to create a gMSA
A gMSA is a type of managed service account (MSA) that provides a computer identity to services running on different computers in the same domain. It is used to simplify the management of accounts and passwords for services running on multiple servers. To create a gMSA, there are three steps required:
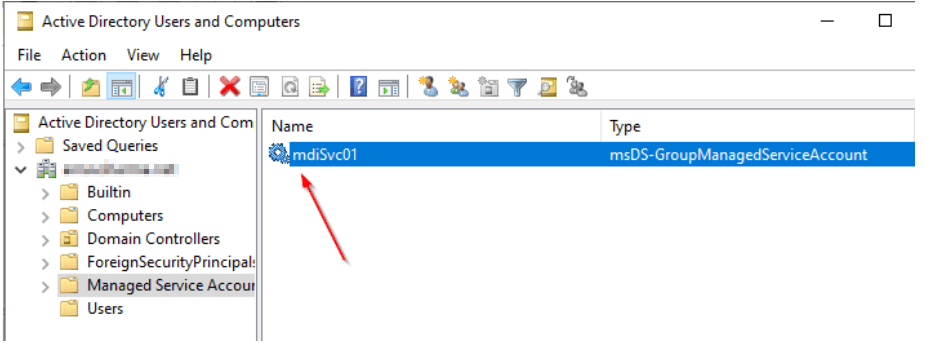
1. Create an Active Directory container to store the account information. This can either be done using the Active Directory Users & Computers MMC snapshot or Windows PowerShell commands.
2. Create an MSA using either the New-ADServiceAccount cmdlet in Windows PowerShell (PowerShell Modules need to be installed) or through the Managed Service Accounts MMC snap-in. Here, you will specify a name and password for the gMSA while also providing options such as whether it should replicate all domain controllers within its forest or just specific ones and if it should have any special permissions associated with it.
3. Configure each server that needs access to use this gMSA by setting up their local security policy accordingly with either Windows group policy object (GPO) or manually via registry edits. Once completed, services can be configured to run as this new gMSA account instead of having individual accounts for each service on each server, reducing administrative overhead significantly.
Best Practices for Using gMSA
Best Practices for Using gMSA are important when implementing this technology in an enterprise environment. First, it is important to ensure that the environment meets all the necessary requirements and security standards before deploying gMSA. It is also important to properly configure the gMSA account and its associated service accounts and ensure they are secure and kept up-to-date. Additionally, administrators should ensure that any changes made to the gMSA configuration or service accounts are tested thoroughly before being deployed in production environments. Finally, it is essential to regularly audit the environment and check for any potential issues with using this technology. Following these best practices will help ensure that gMSA is used securely and effectively within an enterprise environment.
Security Considerations
Security considerations for gMSA are important factors to consider when implementing and managing a gMSA.
- It is important to ensure that the security of the gMSA is managed properly, which includes setting up strong passwords, encryption, and other access control measures.
- It’s also important to monitor the system for any unauthorized changes or activities.
- As gMSAs can be used across multiple systems, additional safeguards should be implemented to ensure that only authorized people have access.
- Additionally, regular audits should be conducted to ensure that all requirements are met and that no unauthorized changes have been made.
- Finally, best practices such as using two-factor authentication should be implemented to protect the gMSA from malicious activity further.
Using a Group Managed Service Account (gMSA) is an important security consideration for any organization. gMSAs are managed service accounts that can be used to run services on Windows Server machines, and they are handled by Windows directory services. They are created in an Active Directory domain and require using Microsoft Key Distribution service for authentication. Setting up the appropriate security group in your Active Directory environment is also important to use the gMSA properly. A gMSA can be set up using the Active Directory PowerShell Module, which allows administrators to configure and manage these accounts easily. With proper security considerations in place, organizations can benefit from the improved security that gMSAs provide while still keeping their systems secure.
Managing gMSAs
Group Managed Service Accounts (gMSAs) are service accounts used to provide managed access to services running on servers in an Active Directory domain. They offer several benefits over traditional service accounts, including automatically updating passwords and managing multiple instances of the same service on different servers. Managing gMSAs properly ensures security, reliability, and efficiency within an organization’s IT infrastructure.
When managing gMSAs there are several key steps to take:
- first, create a dedicated organizational unit (OU) in Active Directory for storing the gMSA objects;
- second, configure the groups associated with each gMSA so that they can access necessary resources;
- third, create the necessary DNS records;
- fourth, assign computers and services to use the gMSAs;
- and finally, configure periodic password management tasks such as resetting passwords every 90 days or enabling automatic password updates when they expire.
It is also important to properly audit all changes made to any existing gMSA objects so that all actions remain secure and compliant with internal policies. Additionally, it is recommended that organizations regularly review their list of active gMSAs for any unnecessary accounts which should be removed or disabled if no longer needed.
Managing group-managed service accounts (GMSAs) is an important part of the system administration process. GMSAs are accounts that are used to provide access to network resources and services in a secure manner; they are created with a unique name for each group, and their passwords are managed by Windows Server. With GMSAs, sysadmins can ensure that every user within a certain group has the same level of access and privileges, making it easier to control security. To retrieve the password for a GMSA, sysadmins need to use the command line tool ‘gmsa’, which will allow them to easily support GMSAs without having to manually manage all of the individual users’ accounts within a given group. This helps keep systems secure by ensuring that all users have the same level of access and privileges while also providing sysadmins with an easy way to manage their groups.
FAQ:
Q: What are Group Managed Service Accounts (gMSAs) and how do they differ from regular user accounts in terms of service management?
AA: Group Managed Service Accounts (gMSAs) are a type of domain account introduced in Windows Server 2012, designed to provide automatic password management and simplified service principal name (SPN) management for services running on a server farm. Unlike using regular user accounts as service accounts, gMSAs offer secure password management handled by the Windows operating system, eliminating the need for administrators to manually manage service account passwords. This makes gMSAs more secure and easier to manage compared to traditional user accounts used for services.
Q: How can one manage Group Managed Service Accounts and what tools are available for this purpose?
AA: To manage Group Managed Service Accounts (gMSAs), you can use tools like Server Manager and PowerShell scripts. The management process includes creating a group in Active Directory for the gMSA, installing the gMSA on the necessary computer accounts where gMSAs are installed, and configuring the service instances to be managed by the gMSA. Administrators can also delegate gMSA management to other administrators, enhancing security and account management efficiency. Windows Server 2012 and later versions support gMSAs, providing interfaces for their management.
Q: What is the process to retrieve and manage the password of a gMSA?
AA: The password of a Group Managed Service Account (gMSA) is managed automatically by the Windows operating system, providing secure gMSA password management. Administrators do not need to manually handle the password. However, if there’s a need to retrieve the password, specific permissions are required. Only accounts that are allowed to retrieve the password and have the necessary Active Directory permissions can query the password information from Active Directory. This process is part of securing group managed service accounts, ensuring that only authorized personnel can access sensitive information.
Q: How do you use gMSAs on servers, and what are the benefits compared to other account types?
AA: To use a gMSA on servers, administrators first create a gMSA in Active Directory, and then install the gMSA on the server where it will be used. The services on the server are then configured to run under the gMSA. This setup, compared to using personal accounts as service accounts, offers several benefits such as automatic password management, the ability to delegate the management of these accounts, and enhanced security. gMSAs eliminate the risks associated with administrators using their personal accounts for service accounts or service accounts with static passwords.
Q: Can you explain the process of finding and installing gMSAs on a server farm?
AA: To find and install gMSAs on a server farm, administrators can start by searching for existing gMSAs in the Managed Service Accounts folder in Active Directory. Once identified, the gMSA can be added to the necessary server or computer accounts where gMSAs are to be installed. This process is typically done using tools like Server Manager or PowerShell scripts. The gMSA will then be associated with specific service instances on those servers, providing benefits such as automated password management and improved security for services running across the server farm.
Q: What are the requirements for a server to support gMSAs, and how does it improve security management?
AA: For a server to support gMSAs, it needs to be updated to Windows Server 2012 or later and be part of a Windows Server 2012 domain controller or newer. This update ensures that the server has the necessary features to handle gMSA password management and SPN management. The use of gMSAs improves security management by automating password updates and reducing the risk of password-related security breaches. Additionally, gMSAs provide the ability to delegate account management, further enhancing security and administrative efficiency.
Q: How does Active Directory support and interact with gMSAs?
AA: Active Directory supports gMSAs by storing their information as a specific object type in its database. This includes data related to their password and SPN configurations. Active Directory also manages the automatic password updates for gMSAs and provides administrators with the necessary permissions to administer these accounts. The interaction between gMSAs and Active Directory is crucial for the security management of these accounts, ensuring that password access and high-risk permissions are tightly controlled and monitored.
Q: What steps are needed to create and administer a Group Managed Service Account (gMSA)?
AA: To create and administer a gMSA, you first need to create a group in Active Directory for the account. Then, you must use the ‘New-ADServiceAccount’ cmdlet in PowerShell to create the gMSA. After creation, you can add the gMSA to the Managed Service Accounts Organizational Unit (OU) and grant permission to specific servers or server farms to use it. The gMSA will be created with a managed domain account and can be further managed through Active Directory tools and PowerShell scripts for tasks such as updating its security settings.
Q: How does Windows Server 2016 enhance the functionality of gMSAs compared to earlier versions?
AA: Windows Server 2016 introduced significant enhancements in the functionality of gMSAs. It improved the security and management aspects by providing better integration with Active Directory, enabling more efficient management of account passwords and permissions. This version also introduced features to detect gMSA password access and high-risk permissions, enabling administrators to execute specific actions when gMSA abuse is detected. These improvements made gMSAs more robust and secure for managing service accounts in a Windows environment.
Q: What are the security benefits of using gMSAs for service accounts in a server environment?
AA: The security benefits of using gMSAs for service accounts in a server environment include automatic password management, which reduces the risk associated with manual password updates and potential exposure. The gMSA ensures that service account passwords are regularly updated and secured without administrator intervention. Additionally, the use of gMSAs restricts the ability to retrieve the password only to accounts that are explicitly granted permission, thereby enhancing the overall security posture. This setup prevents the misuse of service accounts and strengthens the security of server operations.
Q: How can administrators effectively find and manage existing gMSAs in their network?
AA: Administrators can effectively find and manage existing gMSAs in their network by using tools like Server Manager and PowerShell. They can run specific PowerShell commands like ‘Get-ADServiceAccount’ to find gMSAs within their Active Directory environment. For management, administrators can use the ‘Set-ADServiceAccount’ cmdlet to update gMSA properties or delegate management to other administrators. This process allows for efficient oversight and control over the gMSAs deployed across the network.
Q: What are the best practices for securing gMSA passwords and managing related permissions?
AA: Best practices for securing gMSA passwords and managing related permissions include enabling the ‘Audit Directory Service Access’ policy for tracking access to gMSAs in Active Directory. Administrators should also regularly review and update Active Directory permissions related to gMSAs to ensure only authorized personnel have access. Additionally, implementing security measures to detect unauthorized gMSA password access and high-risk permissions is crucial. Regular audits and reviews of the security settings associated with gMSAs help maintain a robust security posture.
Q: Can you describe the process to grant and administer permission to query gMSA passwords in Active Directory?
AA: To grant and administer permission to query gMSA passwords in Active Directory, an administrator needs to first identify the accounts that require access. Using Active Directory tools, the administrator can then set the appropriate permissions on the gMSA object, allowing these selected accounts to retrieve the password. This is typically done by modifying the security settings of the gMSA in Active Directory Users and Computers or using PowerShell scripts. It is important to carefully manage these permissions to ensure that only authorized personnel can access gMSA passwords, maintaining security and compliance.
Q: What are the advantages of using gMSAs over standalone managed service accounts (sMSAs) in large-scale environments?
AA: The advantages of using gMSAs over standalone managed service accounts (sMSAs) in large-scale environments include centralized management and scalability. gMSAs provide the ability to use a single account across multiple servers, which is particularly beneficial in server farms or large-scale server environments. This contrasts with sMSAs, which are limited to a single server. gMSAs also offer more efficient management capabilities, allowing administrators to manage service accounts across multiple servers from a central location, thus reducing the administrative overhead and improving operational efficiency in larger networks.