Last Updated on July 18, 2024 by Arnav Sharma
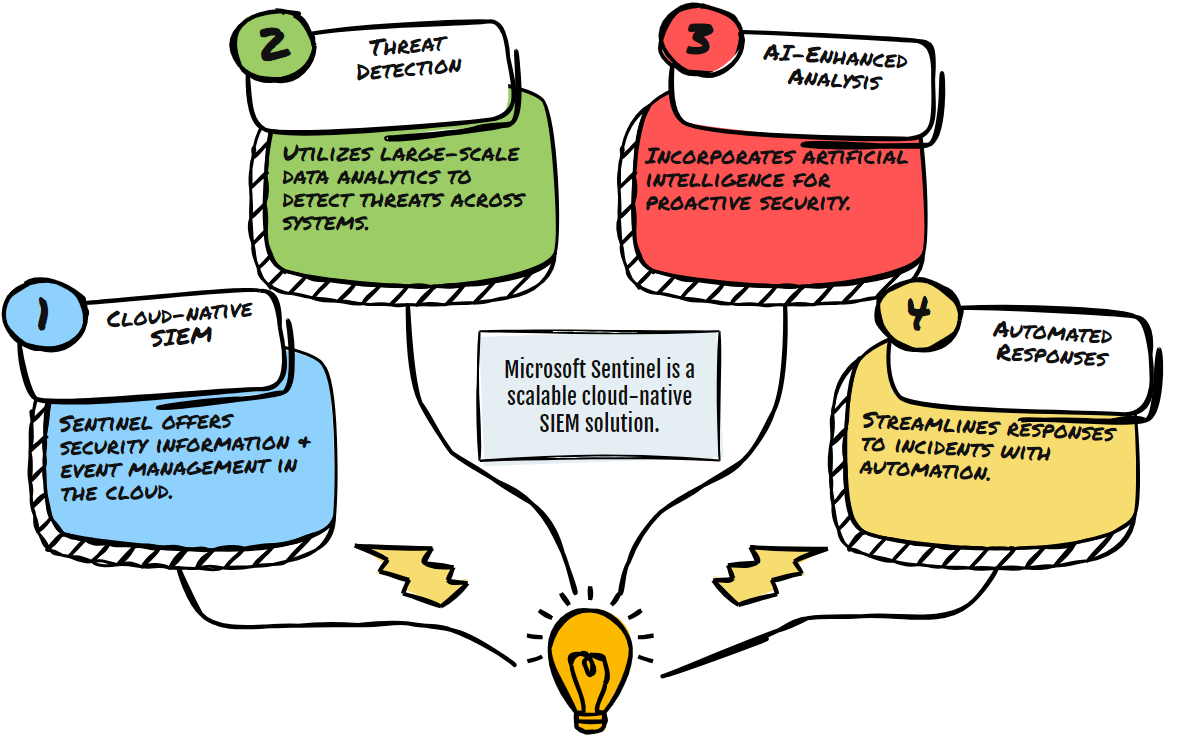
Microsoft Sentinel is a cutting-edge SIEM (Security Information and Event Management) tool designed for modern security needs. It provides a cloud-native solution that integrates various data sources, both on-premises and in the cloud, to offer a comprehensive platform for security monitoring, threat detection, and incident response.
Key Features of Microsoft Sentinel
1. Data Collection: Microsoft Sentinel simplifies the collection of security data from various sources through its out-of-the-box data connectors. These connectors allow for real-time integration with Microsoft products, Azure services, and third-party solutions. Users can also create custom connectors for unique sources.
2. Threat Detection: Leveraging advanced analytics and Microsoft’s vast threat intelligence, Sentinel helps detect new threats and minimize false positives. It employs sophisticated algorithms and integrates with frameworks like MITRE ATT&CK to help users understand and visualize threat tactics and techniques.
3. Threat Investigation and Hunting: Sentinel facilitates proactive threat hunting and deep investigation capabilities, utilizing AI and machine learning to sift through large datasets to identify anomalies and potential threats. It supports the use of Jupyter notebooks within the Azure ecosystem for more complex data analysis and visualization tasks.
4. Incident Response: Automation is at the heart of Sentinel’s incident response. It uses Azure Logic Apps to create playbooks that automate the response process, ensuring that actions like alert triage and incident escalation are handled swiftly and efficiently.
Deployment and Best Practices
Deployment Strategies: When deploying Microsoft Sentinel, consider the architecture of your workspace. Decisions about whether to separate data types and how to manage billing and resource allocation are crucial. Designing your workspace to efficiently handle your specific data load can significantly impact performance and cost.
Best Practices:
- Regular Monitoring and Updates: Regularly review and update your data connectors and analytic rules to ensure they are functioning correctly and are aligned with the latest security protocols.
- Optimize Data Management: Efficient data management is critical. This involves normalizing and parsing data to ensure it is ready for analysis and ensuring that data retention policies comply with your organization’s standards and regulations.
- Cost Management: Understanding and managing costs is crucial, especially when operating at scale. Microsoft Sentinel offers tools and calculators to help estimate and manage these expenses effectively.
Deployment Overview
Deploying Microsoft Sentinel involves several key steps that ensure its integration into your security operations is seamless and effective:
- Initial Setup: Begin by setting up your Log Analytics workspace, which will serve as the foundation for data collection and analysis in Sentinel.
- Data Connectors: Install and configure data connectors to stream data from your various data sources into Sentinel. This includes connectors for Microsoft services and third-party applications.
- Detection Rules: Configure detection rules to automate the process of identifying potential security threats based on the incoming data.

Prerequisites
Before deploying Microsoft Sentinel, certain prerequisites must be met:
- Azure Subscription: An active Azure subscription is required to host and manage the Log Analytics workspace.
- Permissions: Adequate permissions in Azure AD are necessary to install and configure Sentinel, including contributor roles on the subscription and specific roles for managing Log Analytics and Sentinel itself.
- Network Configuration: Ensure that your network settings, such as firewalls and security groups, allow for the proper flow of data to Sentinel.
Best Practices for Effective Use
To maximize the effectiveness of Microsoft Sentinel, follow these best practices:
- Regular Updates: Consistently update and review your data connectors and analytics rules to align with new threats and changes in your IT environment.
- Workspace Hygiene: Regularly audit your Sentinel environment to check for misconfigurations or unused resources that could lead to inefficiencies or security gaps.
- Role-Based Access Control: Implement strict access controls to ensure that only authorized personnel have access to sensitive security information and capabilities within Sentinel.

Architecture and Workspace Design
The architecture of your Microsoft Sentinel environment is crucial for optimized performance and cost management:
- Data Segregation: Consider creating multiple workspaces for different data types or departments to isolate and manage data more effectively.
- Scalability: Design your environment to scale up or down based on your needs, utilizing Azure’s cloud scalability features to handle varying loads of data and analysis.
- Integration: Ensure that Sentinel is well-integrated with other tools and platforms in your security ecosystem, such as threat intelligence platforms and automated response systems.

Billing, Cost, and Tiers
Understanding and managing the costs associated with Microsoft Sentinel is essential:
- Pricing Model: Microsoft Sentinel uses a pay-as-you-go pricing model based on the volume of data ingested for analysis and stored in the Log Analytics workspace.
- Cost Optimization: Utilize tools like the Microsoft Sentinel pricing calculator to estimate costs and identify potential savings. Consider using reserved capacities for longer-term cost savings.
- Commitment Tiers: Microsoft offers commitment tiers that provide cost reductions based on the volume of data you commit to using in Sentinel over a certain period. These tiers can significantly reduce the overall cost of operation if your data ingestion volume is high and predictable.
Cloud Support
Microsoft Sentinel is designed to support various cloud environments, enhancing its flexibility and utility across different platforms:
- Multi-Cloud Capabilities: Sentinel can collect data from various cloud providers, not just Azure, allowing for comprehensive visibility across your entire cloud infrastructure.
- Cloud-Agnostic Tools: The use of cloud-agnostic tools and features within Sentinel ensures that security teams can manage and respond to threats across any cloud platform, providing a unified security management experience.
Enabling Microsoft Sentinel and Key Features
- Setup on Log Analytics Workspace: Begin by integrating Microsoft Sentinel with your Azure environment through a Log Analytics workspace. This step is crucial as it lays the groundwork for the operational capabilities of Sentinel, ensuring that all subsequent features and tools function seamlessly.
- Activating Health and Audit Features: Enable health and audit monitoring early in the setup to maintain system integrity and security. These features track the health of Microsoft Sentinel and alert administrators to any operational issues or unauthorized access attempts, providing a crucial layer of security.
- Enabling Solutions and Content: Select and activate specific solutions and content that align with your data sources. This process involves identifying which types of data you need to monitor and ensuring that Microsoft Sentinel is configured to ingest and analyze this data effectively.
Onboarding to Microsoft Sentinel
- Workspace Selection: Add Microsoft Sentinel to an existing workspace or create a new one through the Azure portal, depending on your organizational needs. This flexibility allows for tailored security operations setups.
- Solution Installation and Data Connectors: Install necessary solutions from the content hub, such as the Azure Activity solution, and configure the appropriate data connectors. These connectors are essential for data ingestion, enabling Microsoft Sentinel to collect data from various sources for monitoring and analysis.

Configuring Microsoft Sentinel Content
- Data Connectors Configuration: Properly configure data connectors based on your selected data sources. This might include setting up both out-of-the-box and custom connectors to ensure comprehensive data coverage.
- Analytics Rules Setup: Develop and configure analytics rules that automate the detection of threats across your data. These rules help sift through vast amounts of data to identify potential security incidents quickly.
- Automation Rules and Playbooks: Establish automation rules to define automated responses to detected threats. Additionally, implement playbooks to orchestrate these responses, enhancing the efficiency of your security operations.
- Workbooks for Data Analysis: Utilize workbooks to create detailed visual reports and data analyses within Microsoft Sentinel. These tools offer customizable options for visualizing and interpreting security data, helping stakeholders make informed decisions.

Detailed Configuration Examples for Microsoft Sentinel
1. Data Connectors Configuration
Data connectors in Microsoft Sentinel serve as the integration points that bring external data into the platform. Here’s how you can configure them:
Example with Azure Activity Connector:
- Out-of-the-box Connector: To set up an out-of-the-box connector like the Azure Activity connector, you would:
- Navigate to Microsoft Sentinel > Data connectors in the Azure portal.
- Select the Azure Activity connector from the list and view the connector page.
- Ensure prerequisites such as appropriate permissions and existing Azure subscriptions are met.
- Click “Open connector page” to configure and enable it, following specific instructions for collecting logs from Azure activities.
Custom Connector Example:
- Custom Syslog Connector: If you’re setting up a custom connector for Syslog:
- First, ensure that your Syslog server is configured to forward logs to the Azure Log Analytics workspace.
- In Microsoft Sentinel, create a new data connector for Syslog by specifying the server details and log types you wish to ingest.
- Customize parsing rules to align with the structure of your Syslog data, ensuring relevant fields are extracted and normalized for analysis.

2. Analytics Rules Setup
Analytics rules in Microsoft Sentinel help detect threats by applying logic to the ingested data. Here’s how to set them up:
Example of Creating a Scheduled Query Rule:
- Navigate to Microsoft Sentinel > Analytics.
- Click “+ Create” and select “Scheduled query rule.”
- Define the rule logic by specifying a Kusto Query Language (KQL) query that identifies potential security threats, such as multiple failed login attempts from a single IP address.
- Configure the rule trigger conditions, such as the frequency of the query execution and the thresholds that must be met for an alert to be triggered.
- Define the alert details, including severity, tactics, and a description to help responders understand the context.
3. Automation Rules and Playbooks
Automation rules and playbooks in Microsoft Sentinel help streamline responses to detected threats.
Example of Setting Up an Automation Rule:
- Navigate to Microsoft Sentinel > Automation.
- Create a new rule and set the triggering condition, such as an alert with a high severity level.
- Define actions such as sending an email notification, firing off a webhook to an external ITSM tool, or invoking a playbook.
Playbook Example for Phishing Response:
- Create a playbook in Microsoft Sentinel using Azure Logic Apps.
- Define the playbook to trigger on phishing-related alerts.
- Set up actions within the playbook, such as:
- Parsing the alert to extract email sender and subject.
- Checking the sender against a database of known malicious actors.
- If matched, automatically initiating actions like blocking the sender, notifying security teams, and marking the email for deletion.

4. Workbooks for Data Analysis
Workbooks provide visual data analysis capabilities within Microsoft Sentinel.
Example of Creating a Security Dashboard:
- Navigate to Microsoft Sentinel > Workbooks.
- Click “+ Add workbook” to create a new one.
- Use the workbook editor to add visual components such as charts, tables, and timelines.
- Construct queries using KQL to pull in data, such as sign-in logs, threat indicators, or incident summaries.
- Arrange these components to display key metrics like alert trends, user risk profiles, or geographic distributions of threats.
Managing Multiple Workspaces and Tenants
- Using Workspace Manager: Leverage Microsoft Sentinel’s workspace manager feature for handling multiple workspaces or tenants. This tool is particularly useful for larger organizations or those with complex structures, allowing centralized management and standardized security practices across all units.
- Grouping and Content Management: Organize workspaces into groups based on specific criteria such as business function or geography. Manage content deployment across these groups to ensure consistency and compliance in security operations.

Data Retention and Archival
- Setting Retention Policies: Configure data retention policies in the Log Analytics workspace to manage how long data is stored based on compliance and operational needs. Adjust these settings to balance the necessity for historical data access with cost and space considerations.
- Archival Strategies: Implement archival strategies to maintain access to older data without incurring high costs. This involves setting up systems to move older data to less expensive storage solutions while ensuring it remains accessible for future analysis.
FAQ: Getting Started with Sentinel
Q: What is the function of a connector in data management?
A: A connector facilitates the integration and transfer of data between different systems, applications, or services, ensuring seamless data flow.
Q: What is a data connector?
A: A data connector is a tool or software component that connects different data sources, allowing them to communicate and exchange information efficiently.
Q: What does it mean to ingest data?
A: To ingest data means to collect and import data from various sources into a central system or database for processing and analysis.
Q: What is a content hub?
A: A content hub is a centralized platform where various types of content, such as articles, videos, and documents, are aggregated, managed, and accessed.
Q: How does a system detect threats?
A: A system detects threats by monitoring activities, analyzing patterns, and identifying anomalies that could indicate potential security breaches or malicious activities.
Q: How is data ingested into Microsoft Sentinel?
A: Data is ingested into Microsoft Sentinel through data connectors that pull information from various sources, allowing Sentinel to analyze and monitor for security threats.
Q: How can I collect data for analysis?
A: Data can be collected using various tools and methods, including data connectors, manual entry, and automated systems that gather information from different sources.
Q: What are the next steps after completing the initial setup of a system?
A: The next steps typically involve configuring settings, importing data, running initial tests, and beginning regular monitoring and analysis.
Q: How is ingested data used?
A: Ingested data is used for analysis, monitoring, and making informed decisions based on the insights derived from the processed information.
Q: Where can I find security updates for my system?
A: Security updates can be found on the official website of the software provider or through the built-in update feature of the system.
Q: Where can I obtain technical support?
A: Technical support can be obtained from the service provider’s support team, online help resources, or built-in support features within the application.
Q: What does built-in mean in the context of software features?
A: Built-in refers to features that are integrated into the software, providing functionality without the need for additional installations or external tools.